view the rest of the comments
Mildly Infuriating
Home to all things "Mildly Infuriating" Not infuriating, not enraging. Mildly Infuriating. All posts should reflect that. Please post actually infuriating posts to !actually_infuriating@lemmy.world
I want my day mildly ruined, not completely ruined. Please remember to refrain from reposting old content. If you post a post from reddit it is good practice to include a link and credit the OP. I'm not about stealing content!
It's just good to get something in this website for casual viewing whilst refreshing original content is added overtime.
Rules:
1. Be Respectful
Refrain from using harmful language pertaining to a protected characteristic: e.g. race, gender, sexuality, disability or religion.
Refrain from being argumentative when responding or commenting to posts/replies. Personal attacks are not welcome here.
...
2. No Illegal Content
Content that violates the law. Any post/comment found to be in breach of common law will be removed and given to the authorities if required.
That means: -No promoting violence/threats against any individuals
-No CSA content or Revenge Porn
-No sharing private/personal information (Doxxing)
...
3. No Spam
Posting the same post, no matter the intent is against the rules.
-If you have posted content, please refrain from re-posting said content within this community.
-Do not spam posts with intent to harass, annoy, bully, advertise, scam or harm this community.
-No posting Scams/Advertisements/Phishing Links/IP Grabbers
-No Bots, Bots will be banned from the community.
...
4. No Porn/Explicit
Content
-Do not post explicit content. Lemmy.World is not the instance for NSFW content.
-Do not post Gore or Shock Content.
...
5. No Enciting Harassment,
Brigading, Doxxing or Witch Hunts
-Do not Brigade other Communities
-No calls to action against other communities/users within Lemmy or outside of Lemmy.
-No Witch Hunts against users/communities.
-No content that harasses members within or outside of the community.
...
6. NSFW should be behind NSFW tags.
-Content that is NSFW should be behind NSFW tags.
-Content that might be distressing should be kept behind NSFW tags.
...
7. Content should match the theme of this community.
-Content should be Mildly infuriating. If your post better fits !Actually_Infuriating put it there.
-The Community !actuallyinfuriating has been born so that's where you should post the big stuff.
...
8. Reposting of Reddit content is permitted, but attribution is not required in any way. No links to Reddit in post body
-If you would like to provide a source link, do so in the comments but not in the post body.
...
...
Also check out:
Partnered Communities:
Reach out to LillianVS for inclusion on the sidebar.
All communities included on the sidebar are to be made in compliance with the instance rules.
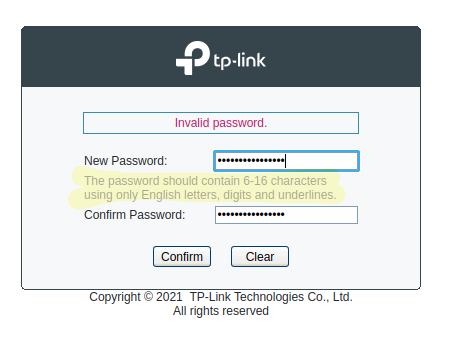
I sort of get it. You don't want to allow the entire work of Shakespeare in the text field, even if your database can handle it.
16 characters is too low. I'd say a good upper limit would be 100, maybe 255 if you're feeling generous.
The problem is that you (hopefully) hash the passwords, so they all end up with the same length.
At minimum you need to limit the request size to avoid DOS attacks and such. But obviously that would be a much larger limit than anyone would use for a password.
Also rate of the requests. A normal user isn't sending a 1 MiB password every second
What's a sensible limit. 128 bytes? Maybe 64?
I'd say 128 is understandable, but something like 256 or higher should be the limit. 64, however, is already bellow my default in bitwarden
And sure, in theory your hashing browser-side could break if you do that. Depending on how much text the user pastes in. But at that point, it's no longer your problem but the browser's. 🦹
Why are you hasing in the browser?
Also, what hashing algorithm would break with large input?
bcrypt has a maximum password length of 72 bytes.
https://en.wikipedia.org/wiki/Bcrypt#Maximum_password_length
Damm, I legit didn't knew there bcrypt had a length limit! Thank you for another reason not to use bcrypt
Scrypt has the same limit, FWIW.
It doesn't matter too much. It's well past the point where fully random passwords are impossible to brute force in this universe. Even well conceived passphrases won't get that long. If you're really bothered by it, you can sha256 the input before feeding it to bcrypt/scrypt, but it doesn't really matter.
wouldn't you then just break it up into chunks of 72 bytes, hash them individually, and concatenate the hashes? And if that's still too long, split the hash into 72 byte chunks and repeat until it's short enough?
I don't know the specifics behind why the limit is 72 bytes, but that might be slightly tricky. My understanding of bcrypt is that it generates 2^salt different possible hashes for the same password, and when you want to test an input you have to hash the password 2^salt times to see if any match. So computation times would get very big if you're combining hashes
Why would you not hash in the browser. Doing so makes sure the plaintext password never even gets to the server while still providing the same security.
Edit: I seem to be getting downvoted... Bitwarden does exactly what I described above and I presume they know more than y'all in terms of security https://bitwarden.com/help/what-encryption-is-used/#pbkdf2
Because then the hash is the password. Someone could just send the hash instead of trying to find a password that gets the correct hash. You can't trust the client that much.
You can hash the password on both sides to make it work; though I'm not sure why you'd want to. I'm not sure what attack never having the plain text password on the server would prevent. Maybe some protection for MITM with password reuse?
Because then that means you don't salt your hashes, or that you distribute your salt to the browser for the hash. That's bad.
You could salt it. Distributing a unique salt doesn't help attackers much. Salt is for preventing precomputing attacks against a whole database. Attacking one password hash when you know the salt is still infeasible.
It's one of those things in security where there's no particular reason to give your attacker information, but if you've otherwise done your job, it won't be a big deal if they do.
You don't hash in the browser because it doesn't help anything.
It helps against the server being able to read the password, so a bad actor (either the website itself or after a hack) could read your password. Which isn't bad if you're using good password hygiene with random passwords, but that sadly is not the norm.
It doesn't. It just means the attacker can send the hash instead of the password.
For that particular website yes, but a salted client side hash is worthless on a different website.
Edit: plus even unsalted it would only work if the algorithm is the same and less iterations are done
If the end user is reusing passwords. Which, granted, a lot of people do.
On the flip side, we're also forcing the use of JavaScript on the client just to handle passwords. Meanwhile, the attack we're protecting against only works for reused passwords, and the attacker is inside the server and can see the password after transport layer encryption is removed. This is a pretty marginal reason to force the complexity of JavaScript.
With comments like this all over public security forums, it's no wonder we have so many password database cracks.
Per your edit, you're misunderstanding what Bitwarden does and why it's different than normal web site password storage.
Bitwarden is meant to not have any insight into your stored passwords what so ever. Bitwarden never needs to verify that the passwords you've stored match your input later on. The password you type into Bitwarden to unlock it is strictly for decrypting the database, and that only happens client side. Bitwarden itself never needs to even get the master password on the server side (except for initial setup, perhaps). It'd be a breach of trust and security if they did. Their system only needs to store encrypted passwords that are never decrypted or matched on their server.
Typical website auth isn't like that. They have to actually match your transmitted password against what's in their database. If you transmitted the hashed password from the client and a bad actor on the server intercepted it, they could just send the hashed password and the server would match it as usual.
If you hash in the browser it means you don't salt your hash. You should absolutely salt your hash, not doing so makes your hashes very little better than plaintext.
There's nothing stopping a browser from salting a hash. Salts don't need to be kept secret, but it should be a new random salt per user.
That's not true. If they send hashed password you could salt/hash again on server if you're trying to keep the salt "secret". Their hash should always be the same if they've submitted the same password. You'd just be hashing a hash in that case... but it's the same premise.
The eBay password limit is 256 characters.
They made the mistake of mentioning this when I went to change my password.
Guess how many characters my eBay password has?
-1?
Damn signed bytes!
0*
Just paste it in here and I count the characters for you.
69
You don't store the original text. You store the hash of it. If you SHA512 it, anything that's ever given in the password field will always be 64Bytes.
The only "legit" reason to restrict input to 16 character is if you're using an encryption mechanism that just doesn't support more characters as an input. However, if that's the case, that's a site I wouldn't want to use to begin with if at all possible.
The resulting hash will always be the same size, but you don't want to have an unlimited upper bound otherwise I'm using a 25GB blueray rip as my password and your service is going to have to calculate the hash of that whenever I login.
Sensible upper bounds are a must to provide a reliable service not open to DDOS exploits.
If I choose to make you hash it in browser first... Then I simply don't care do I? I can hash/salt again when I get your hash. Edit: There are other answers to the "DDOS problem" that don't require upper bounds.
You can make a client hash it, but if you don't reject large inputs to your API a client can send enough data to DOS you anyway.
And a meteor can hit my server the exact time you send your hash which will DOS you/others as well. What's your point.
The thread is talking about what it takes to store passwords. There is not DOS potential in a well designed system. Just because you want to arbitrarily conjure up bullshit doesn't make that any less true.
Rejecting large inputs != disallowing users to have large passwords. Why are you attempting to straw-man me here?
You were saying the input size doesn't matter because you only store the hash which is always the same size. What I'm saying is that the input size really does matter.
You absolutely should set upper limits on all input fields because it will be abused if you don't. Systems should validate their inputs, passwords included
And I showed you a way that we can make it so it doesn't matter.
Force local hash -> Hash/salt what you get. Password can be a million characters long. You'll only ever get like 128 characters.
Nothing I talked about said to not validate inputs. Just that we don't have to limit a persons password selection.
I'll admit I kind of typed this without thinking it through. In a secured site, the password would be hashed and salted before storing in the database.
Depending on where you're doing the hashing, long strings might still slow you down. That being said, from a security standpoint, any gain in entropy by adding characters would be negligible past a certain point. I don't remember what that number is but it certainly isn't in the thousands.
That would be completely based on the hash being used. In the example above I showed SHA512 which is 64Bytes. If we're using ASCII (7 bit per character) as our input then 64 Bytes is just over 73(73.1428...) characters. After that you're losing data in the hashing process and by that effect it would be negligible... (There's some wiggle room here in that we can't type hidden ASCII characters so some passwords over 73 characters would fill those spaces... but detecting collisions is silly and non-trivial... better to just not worry about those at all.)
Extended ASCII would be same premise, just 64 characters instead of 73.
The reality is that nobody is using much more than 64 Bytes for their hashing algorithm for passwords... 64 characters is a good number to max out most of them. Databases don't need to store much at all regardless of the length of your actual password. If you're developing an app you can set the database to limit based on the algorithms you're using. If you have no idea what the web-dev will actually use... then 128 characters on the database field is probably pretty safe (88 I think if storing as Base64, 128 if storing in Hex. Could be off by one here.) and literally trivial to store. The point being that even if every one of your users submitted 10000 character long passwords... that's irrelevant and trivial for storage as hashes.
There's a more practical limit. Using US standard keyboard symbols, a 40 char password is about as secure as a 256-bit block cipher key. That's impossible to break due to thermodynamic limits on computing.
The reason to put a high char limit is to mitigate DoS attacks. It can still be a few hundred chars.
you might compare 1,000 to 10,000, but more like 0.1% to 0.01%
meaning of this? no. bad grammar.
Even 255 bytes with 10 million entries is only ~2.6GB of data you need to store, and if you have 10 million users the probably $1 a month extra that would cost is perfectly fine.
I suppose there may be a performance impact too since you have to read more data to check the hash, but servers are so fast now it doesn't seem like that would be significant unless your backend was poorly made.