I work in a HIPAA-covered industry and if our AWS and GCP buckets are insecure that's on us. Fuck Amazon, but a hammer isn't responsible for someone throwing it through a window and a cloud storage bucket isn't responsible for the owner putting secret shit in it and then enabling public access.
Yeah I hate Amazon as much as the next person, but this is a people/process problem, not an Amazon problem. Amazon doesn't know or care what you put into an AWS bucket (within reason, data tracking, etc, blah blah blah). People taking classified documents and uploading it to an Internet-connected cloud service is procedurally wrong on so many levels.
What kills me about S3 is that the use cases for publicly accessing S3 contents over HTTP have got to be vanishingly small compared to every other use of the service. I appreciate there's legacy baggage here but I seriously wonder why Amazon hasn't retired public S3 and launched a distinct service or control for this that's harder to screw up.
Public access is disabled by default and it warns you when you enable it. How much more idiot proof does it need to be?
Wouldn't say so, loads of people and organisations use it as a pseudo-CDN of sorts AFAIK
Amazon is only doing what someone told it to do. This is improper handling of documents and not a problem with Amazon itself.
Such examples of OpSec competence make it easy to dismiss the majority of government conspiracy theories IMHO.
I go back to the veteran comedian every time.
We can't even stop our privates from telling their stripper girlfriend about the mission they're going on the next day, and people think there's a giant conspiracy out there where nobody talks...
Then there's the Warrantless Wiretap program under the Bush Administration. Cheney kept the authorization memo in his personal lawyer's safe. Only 7 people knew it existed. Shit still leaked.
Only 7. That’s perfect. I forget who said “three may keep a secret if two are dead” but of all the mustache twirling pricks in that admin, Cheney should have known.
Edit: it’s Ben Franklin’s joke, apparently. I doubt he’d mind.
They dropped this to make themselves look incompetent!
4D chess by the deep state!
"No! This is not how the game is meant to be played."
Compartmentalisation helps
If no one actually knows the plan other than the guy in charge, no one can leak the plan:
An example of compartmentalization was the Manhattan Project. Personnel at Oak Ridge constructed and operated centrifuges to isolate uranium-235 from naturally occurring uranium, but most did not know exactly what they were doing. Those that knew did not know why they were doing it. Parts of the weapon were separately designed by teams who did not know how the parts interacted.
To be fair, it’s probably more about the IT contractors and consulting firms that didn’t implement security policies or configurations correctly on the S3 buckets for the governments they’re working for. The AWS products aren’t opening up things to the public internet without auth. Which I bet most of you knew.
Example: Accenture left a trove of highly sensitive data on public servers (2017)
I added more JPEG for OP:

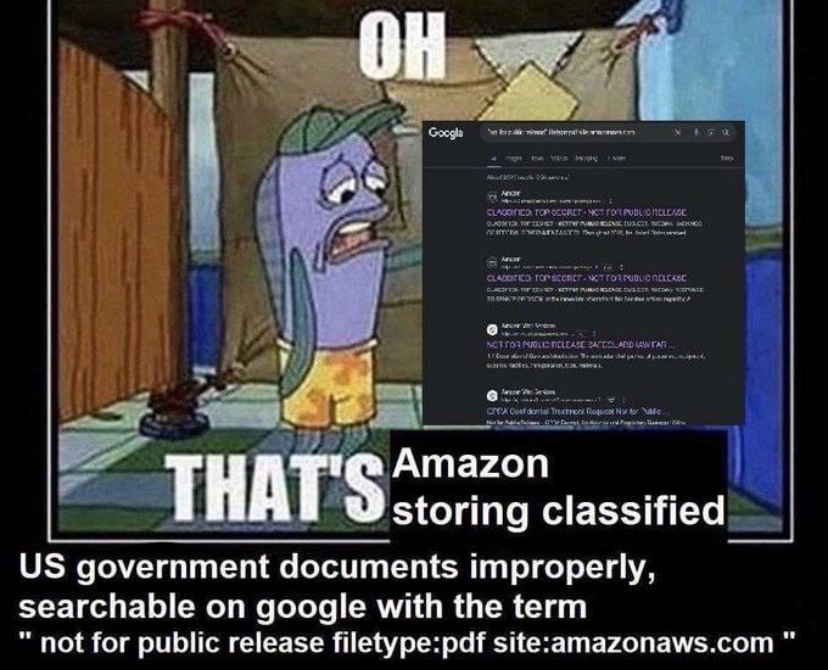
Aaand that search query got me some files with the top secret flag. Fortunately, they seem to be internal memos on things that are already known to the public, so nothing too immediately dangerous.
My big question is, why in the ever-loving fuck are these files outside of SIPRNET?
Cloud cloud cloud, cloudy cloud, cloudy cloudy cloud cloud.
-Management
Cloudorporate is confused!
Cloudorporate hurt itself in its confusion!
Contractors and third parties with security clearance. Did you really think any US government agency actually tightened things down properly after Snowden?
Is it illegal to have these or just distribution is illegal? I'm worried about the implications of you downloading but it isn't like anyone will care.
As for how they got there, perhaps via scan-to-email from the Mar-a-Lago copy- and bathroom.
This shit has been happening for far far longer than cheeto. It's bipartisan military organization incompetence, and the exact issue that allowed the Snowden leaks to occur.
The markings tell people with clearance how to handle the documents more than anything else. You have no way of knowing if it's a legit marking.
Obligatory, I am not a lawyer.
If random citizen finds it on the street they can't be punished for having it. But the government can repossess the document at any time.
"cloud first" is a mantra that not even the FedGov can refuse.
Mostly cuz the largest, data mining, and ad-driven companies in the world told them it was better.
Okay, the question I have, is why any government from a developed country would ever use something like AWS or something that everyone can obtain access to rather than making their own private solutions to these problems?
It's easier to hire someone who knows aws than to train someone on your custom thing. I don't really agree, but that's mostly the reasoning.
Not to mention in house solutions are basically guaranteed to cost more than AWS to get something even close to as comparable. A basic service like Lambda is complex as fuck and has had billions of dollars poured into making it what it is today.
In Portuguese: https://www.serpro.gov.br/menu/noticias/noticias-2023/serpro-lanca-nuvem-de-governo
Brazillian government launched its own cloud service to support the government agencies, everything stored and administer in Brazilian territory, making it independent from private companies and international governments.
🎉 Hooray!
Another question could be : which developed country is not yet using the popular AWS already and why ?
For example : https://press.aboutamazon.com/2023/10/amazon-web-services-to-launch-aws-european-sovereign-cloud
Customers, AWS Partners, and regulators welcoming the new AWS European Sovereign Cloud include the German Federal Office for Information Security (BSI), German Federal Ministry of the Interior and Community (BMI), German Federal Ministry for Digital and Transport, Finland Ministry of Finance, National Cyber and Information Security Agency (NÚKIB) in the Czech Republic, National Cyber Security Directorate of Romania, SAP, Dedalus, Deutsche Telekom, O2 Telefónica in Germany, Heidelberger Druckmaschinen AG, Raisin, Scalable Capital, de Volksbank, Telia Company, Accenture, AlmavivA, Deloitte, Eviden, Materna, and msg group
Cloud presents several advantages,and GovCloud is a thing.
Like, Amazon has SCIF cloud offerings. These leaks were cuz some dumbass contractor exposed a repo to the internet
I expect the same reasons they're mostly all using Microsoft Office, Windows, and Active Directory. Because it's cheaper than doing it yourself.
So many of the results I see are incredibly obvious fakes.
What's the over-under on this being a honeypot?
My bets are on ~~"cloud infrastructure is bad for highly secret information" rather than "public web honeypot with zero obfuscation"~~ Edit: likely fake. The sensationalist in me would love it if this was real because it would confirm my "cloud storage bad" biases, but alas, the document markings dont appear to be consistent with my understanding of official US Government confidentiality/secrecy markings
If S3, it's not cloud storage's fault some dummies enable public access to buckets which is disabled by default.
Youre correct it's not the provider's fault, but it's much harder in my very biased opinion to accidentally expose a secure 100% internal intranet than it is to accidentally put a top secret document in a public data bucket.
But it's a moot argument in this case anyway. Fake documents means these are likely exposed just to troll folks like us.
In their defense:
Second result for me was a document about Russian hackers and their demands that we enstate trump as president after he lost.
Yeah i saw this before
Security
Confidentiality Integrity Availability